What Are
Embedded Systems?
Learn about embedded systems and their design and development, from board support packages to modern application development.
What Are Embedded Systems?
Embedded systems are computer systems with dedicated functions that are used in devices, machines, and systems running in multiple market segments. These systems have a wide range of requirements and different levels of complexity. Embedded systems are used in just about all markets.
Embedded systems can be purpose built, with tight integration with their hardware. There are also general-purpose embedded systems that can be programmed to perform multiple functions. Complex embedded systems, such as airplanes, autonomous vehicles, and industrial control systems, require more hardware and software resources to perform their many functions, and these systems often require high-performance processors to run millions of lines of code.
Many types of embedded systems have functional safety requirements. They run mission-critical and safety-critical applications that cannot fail. These devices require an operating system that executes tasks with real-time and deterministic results, and they may require higher levels of security to meet safety requirements.
Although many embedded systems are purpose built, some common characteristics help identify and define their requirements:
- Real time
- Determinism
- Small footprint
- Safety
- Security
- High performance
- Reliability
- Power and size constraints
- Rugged and extreme operation
One of the biggest challenges of building an embedded system is that one size does not fit all. Each device, machine, and system can utilize different combinations of hardware processors, hardware boards, operating systems, and software components. The environment in which the system is deployed can also determine what needs to be built. Each device has its own set of functional requirements to get the job done.
Embedded Systems Architecture
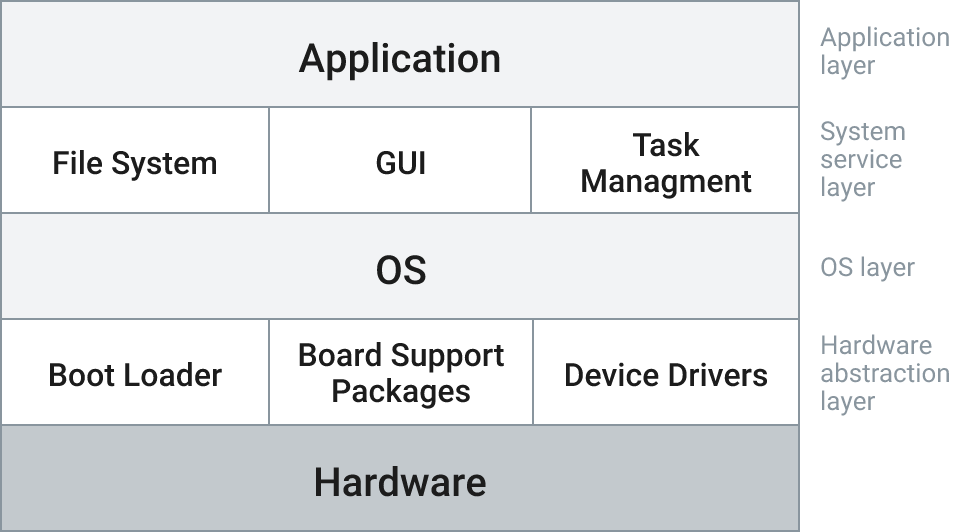
There are five key components to an embedded operating system:
- Hardware processor
- Hardware abstraction layer (HAL)
- Operating system (OS)
- Service layer
- Application layer
1. Hardware Architectures and Processors for Embedded Systems
Embedded systems can utilize CPUs based on 8-, 16-, 32-, and 64-bit processors. They can also use both single core and multi-core processors. Embedded systems with more complex functionality typically utilize 32- and 64-bit single core and multi-core processors. Hardware processor companies design their chips based on a variety of hardware architectures, such as Arm®, Intel® architecture, Power, RISC-V, and Scale.







SINGLE CORE VS. MULTI-CORE PROCESSOR
| SINGLE CORE PROCESSOR | MULTI-CORE PROCESSOR |
|---|---|
|
A single core processor has one core on a chip. It can run and compute only a single function at any one time. Many of the embedded systems deployed today are using single core processors. |
A multi-core processor has two or more separate processing cores or CPUs. Each core can run and compute a single dedicated function. The fastest multi-core processors offer up to 64 cores with 128 threads. |
2. Hardware Abstraction Layer (HAL)
The HAL allows the operating system to interact with the hardware. It defines the set of routines, protocols, and tools needed to allow the operating system and physical hardware to work together. Typical components of the HAL include the board support packages (BSPs), boot loaders, device drivers, and configuration files. The HAL allows the operating system and applications to run regardless of the underlying hardware processor architecture.
Board Support Package (BSP)
BSPs, which include hardware-specific code made up of device drivers and function routines, are crucial to embedded system development.
Every embedded hardware board requires a BSP to allow an operating system to run. Many embedded projects use multiple sourced hardware systems. A different BSP is required for each hardware board and each operating system type running on that board. Some hardware vendors provide standard BSPs for commonly used operating systems such as Linux. Commercial operating system vendors can also provide standard BSPs for some of the popular hardware systems. Many companies customize BSPs to fully leverage the capabilities of the hardware and operating system.
» See the catalog of available BSPs for VxWorks® and Wind River® Linux3. Embedded Operating Systems
The primary software component of embedded systems is the operating system, or OS. The OS is integrated with the underlying hardware chosen for the project and manages the hardware and software resources of the system. It also provides common services to enable applications to easily run with underlying hardware. The OS can manage functions, schedule tasks, maximize performance, respond to interrupts and external I/O, share and protect system resources (such as files), and enable connection to different networks. Operating systems can also provide a layer of security to help protect the device and the data it generates from malicious attacks.
Embedded systems use different types of operating systems:
Real-time operating systems (RTOSes)
Embedded systems have traditionally used real-time operating systems for devices of all kinds. RTOSes provide high performance, a small footprint, low-latency (real-time) responsiveness, and deterministic behavior. Devices and machines with mission-critical, safety-critical, and functional safety requirements rely on an RTOS to execute applications on time and as expected, without fail. VxWorks is an example of a market-leading commercial RTOS.
There are also RTOSes supported by open source community projects including FreeRTOS and Zephyr. FreeRTOS is an RTOS for microcontrollers and microprocessors; Zephyr is another RTOS project architected for small, connected, and resource-constrained embedded devices.
Embedded Linux
Today, Linux is a widely used OS for embedded. Linux is a freely available open source operating system supported by a community of developers. Embedded Linux is used for devices, machines, and systems that do not typically require hard real-time operations and determinism. However, some companies use the pre-empt RT kernel configuration to achieve near real-time performance.
There are a number of community-supported Linux projects organized to address specific industries and market needs. OpenEmbedded is the de facto project for embedded systems development on Linux, and it defines and organizes the Linux packages and resources that are most commonly used with the Yocto Project. The Yocto Project provides a set of tools to help developers build a custom Linux distribution for embedded systems. Many embedded hardware suppliers include support for the Yocto Project as part of their integrated software bundles. This bundled Linux software with specialized hardware is a starting point for an embedded systems project. Additional modifications and optimizations and long-term support and maintenance are typically required.
» Learn more about embedded LinuxWind River is a founding member of the Yocto Project and provides a commercially validated, verified, and supported build system for its customers. Wind River provides a number of Yocto Project Linux BSPs for a variety of hardware boards and processors.
Security and Cybersecurity for Embedded Systems
Just like laptops and mobile phones, embedded systems require features for both device security and cybersecurity. Designing embedded systems with security in mind is a full lifecycle process. It starts before the first line of code is written and ends only when the device is removed from deployment and is inoperable.
Embedded security is a five-point process:
- Secure the development environment: The platform and tools used to build the device must be secure, which means having a secure software factory and infrastructure.
- Secure the device: Security features built into the hardware and operating systems are utilized and enacted. Additional security features, such as kernel hardening and secure boot, may be required.
- Secure the applications: The applications that run on embedded devices can be vulnerable and present a targeted attack surface.
- Secure the data: The intelligent embedded systems deploying today generate an enormous amount of data. This data, whether at rest or in motion, must be secured.
- Engage in ongoing security monitoring: Every deployed embedded device is a potential attack surface. This threat increases exponentially as more and more devices connect to other devices and networks. Continuous monitoring for common vulnerabilities and exposures (CVEs), as well as software updates to fix them, are required to keep devices current and up to date with the latest security patches.

Designing a secure embedded system is a full lifecycle process, starting before the first line of code is written.
Industry and Government Certifications
Many embedded systems require meeting strict guidelines and certifications for safety before they can deploy. Certification requirements can be defined by an industry as well as by a government agency. They can also vary greatly by geographical region.

Many industry-specific certifications can help device manufacturers achieve higher levels of standards. Companies building embedded systems for industrial applications, for example, utilize the expertise of TÜV SÜD, the Technical Inspection Association, to test, inspect, and certify products. Following the TÜV certification process helps ensure that devices comply with safety regulations and quality criteria based on international standards. Companies routinely verify their products to ensure that they are fit for use in the safety environment in which they will deploy.
An example of a government agency that regulates and monitors medical devices is the U.S. Food and Drug Administration, also known as the FDA. The FDA regulates and monitors medical devices to ensure that they comply with applicable standards for operation and safety.
VxWorks is an RTOS that can be used in systems requiring:
- IEC 61508 for industrial functional safety certifiable to SIL 3
- DO-178C for airborne systems certifiable to DAL A
- ISO 26262 for automotive safety systems certifiable to ASIL-D
- IEC 62304 for medical safety requiring class C risk level
Source Code, Binaries, and Containerization
Access to OS source code is an important element for building embedded systems software. Developers need source code to fully understand how the operating system functions. The source code allows developers to configure, build, and compile the operating system based on their project requirements.
Not all embedded designs require access to the source code. Many developers use pre-built binaries of the operating system. Binaries have already been compiled and cannot be modified.
A new trend in embedded software development is containerization. Containers package OS libraries and runtime dependencies into a lightweight executable. Container-based software can run consistently on most operating systems. Both VxWorks and Wind River Linux support the open container initiative (OCI).
Software Compliance
Embedded system software can be required to be standards compliant and adhere to a company’s license compliance policies before it can be commercially deployed. Often an embedded system will be described as being based on industry standards. This means the software adheres to the rules of a well-defined public standard. Software can also be required to be compliant with companies’ software licensing policies. License compliance means the software used for an embedded device includes accurate documentation and proof of licensing agreements, and those license agreements do not contain conditions that violate the policies or practices of the companies using the software. Many embedded developers utilize open source or freely available software for their designs. That software can be anything from a big and complex operating system to a small script. License compliance ensures that copyrighted components are documents and are properly addressed.
Recently, commercial software providers for embedded systems have started to provide a software bill of materials (SBOM). The SBOM lists all the software components, both proprietary and open source. Providing a list of all the components with specific versions allows a software developer to easily locate a problem area when defects are found. The SBOM serves as a supply chain management function for software.
Long-Term Support and Ongoing Maintenance
Embedded systems are built to stand the test of time. It is not uncommon for embedded devices have deployment lifecycles of 5–20 years in the field. Throughout the lifecycle, software can require long-term support and maintenance to ensure that continuous improvements are made to the system. Software updates provide new features, firmware updates, fixes to critical bugs, and security updates. Today, many updates to software can be made over the air (OTA) versus via a human physically updating every device.
4. Embedded Software Services Layer
The software services layer is also referred to as the middleware. This layer supports a variety of value-added services that serve as an interface to the application layer. Common components of the service layer include files systems, graphical user interfaces, the application programming interface (API), and task managers.
5. Application Layer
Embedded systems have been around since software was deployed with hardware for specialized use cases. Over time, embedded systems have evolved to power devices, machines, and systems that require high reliability, real-time performance, and determinism. Many of these systems were built with rigid operational requirements including software footprint constraints, high performance, and the ability to operate in rugged and extreme environments. Embedded systems include:
- Airplanes
- MRI machines
- Telecom systems
- Signaling
- Spacecraft
- Manufacturing and control systems
- Automobile braking systems
- Radar and sonar equipment
- Modems
- Set-top boxes
- Cellular phones
- Robotics
- Satellite systems
- Medical equipment
- Transportation (trains)
- Network equipment
- Communications
- Cameras
Modern Application Development
Developers are dependent on the different programming languages supported by the operating system. Embedded developers traditionally have used C and C++ programming languages. The Linux operating system and some commercial RTOS solutions support a wide variety of programming languages including C, C++17, Ada, Rust, and Python. Embedded systems have also expanded support for different compilers, libraries, and open source tools. Adopting a modern development approach allows greater efficiency and portability. It also provides frameworks to accommodate new requirements for artificial intelligence (AI) and machine learning (ML) (VxWorks supports all of these, as seen in the sidebar).

DevOps and Cloud-Native Development
Within the last few years, embedded developers have moved to more agile software development approaches. Many embedded projects are being built using DevOps infrastructure.
The Internet of Things (IoT)
As embedded systems technology evolved, connectivity, processing power, and lower prices enabled a new category of devices for the Internet of Things. Smaller, lower-cost, network-connected embedded systems became ubiquitous in smart homes, smart cities, and wearable devices. IoT devices leveraged the existing infrastructure to capture different types of data in the environments in which they were deployed.
The Intelligent Edge
The next generation of embedded devices are being built with cloud-native technologies, allowing companies to explore new use cases at the edge of modern networks. Embedded systems are rapidly transforming to create a new class of devices that make up the intelligent edge. Today, embedded systems and the applications they run are leveraging the processing power of the cloud, as well as AI and ML technologies, to enable greater insights and decision-making at the edge, where devices are deployed. The operational and environmental data gathered from the intelligent edge are used to improve functionality, ensure safety, and make real-time business decisions.
How Can Wind River Help?
Wind River Studio is a cloud-native DevSecOps platform enabling software developers to automate the build process and workflows for VxWorks and Wind River Linux runtimes. It includes:
Proven and Commercially Supported Operating Systems
Wind River provides both an RTOS and a verified and validated Yocto Project–based Linux build system.
VxWorks
VxWorks is the industry’s most trusted and widely deployed RTOS for critical embedded systems that must be safe and secure. It delivers a proven, real-time, and deterministic runtime combined with a modern approach for development. Regardless of the industry or device type, companies rely on the VxWorks pedigree of security, safety, high performance, and reliability.
» Learn moreWind River Linux
Wind River Linux is a verified and validated Yocto Project–based Linux build system. Wind River Linux is a commercially supported OS solution that allows embedded developers to customize and build a Linux platform.
» Learn moreProfessional Services
Wind River Professional Services provides embedded developers the help they need at critical points during the development and deployment lifecycle. The Wind River team of embedded experts provides assistance for software architecture and design, customizing and managing Linux platforms, safety certifications, enhanced security, lifecycle management, and resource training.
» Learn moreVirtualization
Wind River Helix™ Virtualization Platform consolidates multi-OS and mixed-criticality applications onto a single edge compute software platform, simplifying, securing, and future-proofing critical infrastructure solutions in the aerospace, defense, industrial, medical, and automotive markets.
» Learn moreSecurity Solutions
Wind River offers a number of built-in security components in both VxWorks and Wind River Linux. Wind River also proactively monitors and alerts customers to security threats and CVEs for all its products. Customers requiring greater security functionality can leverage Wind River Professional Services for design assessments and feature implementations in the OS and applications.
» Learn moreTools: Simulator, Compiler, Eclipse-Based Toolkit
Wind River provides a number of software development tools for the different phases of the product lifecycle:

Wind River development tools address the various lifecycles stages.
Wind River Workbench
Wind River Workbench is an Eclipse-based integrated development environment (IDE).
Wind River Diab Compiler
Wind River Diab Complier helps boost OS and application performance to meet small footprint and quality requirements.
Wind River Simics
Wind River Simics® is a full-system simulator used by software developers to simulate the hardware of complex electronic systems. Simics allows on-demand and easy access to any target system, more efficient collaboration between developers, and more efficient and stable automation. It provides a path to DevOps and continuous integration and deployment (CI/CD).
» Learn more