WIND RIVER STUDIO: DEVELOP
Security
Wind River Studio provides a secure development environment with workflows that help accelerate the creation of innovative and secure embedded products.
A secure software factory frees developers to focus on innovation while ensuring that your company’s intellectual property is protected from external and internal threats.
Wind River® Studio leverages multiple security technologies, including role-based access control, secure account management, information and event logging, and secrets management to secure your development environment. Studio provides developers a protected environment to build secure runtime images and applications.
Wind River Studio Development Security Capabilities
Access Control
Access to and within the environment is authenticated and authorized across all software factory workflows.
Multi-party Approval Process
Administrative functions within the environment require multi-party approvals to maintain continuity within the development team.
Mutually Authenticated Communications
All software factory workflows and communications within the environment are authenticated, authorized, and encrypted.
Security Tooling
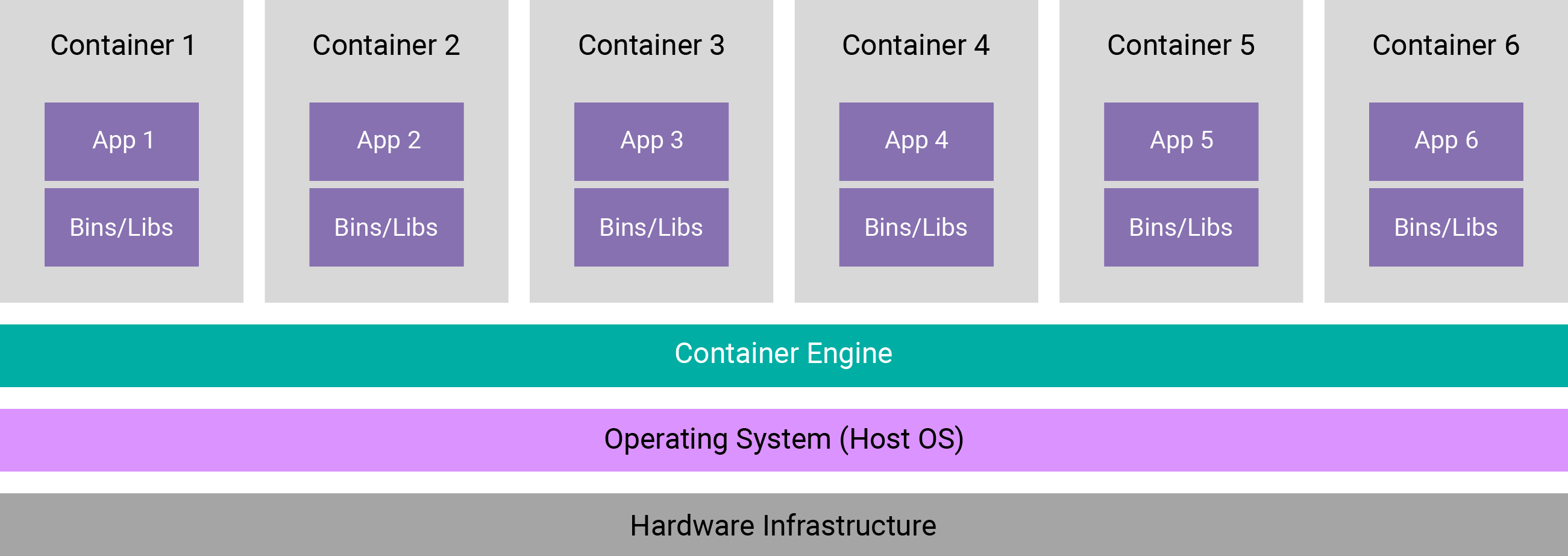
Studio includes a comprehensive suite of container vulnerability scanning, IP compliance, SAST, DAST, and container policy verification.
Secure Supply Chain
Wind River documents every component of the development environment. All open source components that make up the Studio solution are vetted for software provenance, intellectual property issues, and security vulnerability issues.
Edge Device Software Configuration
Studio provides cloud-native tools for configuring edge device platform software for optimal security with capabilities such as secure boot, encrypted communications, and digitally signed software images.
Automated container security scanning
Wind River employs automated container security scanning tools to protect against vulnerabilities in Studio containers. Using tools such as Trivy and Docker Bench for security allows us to identify CVEs in OS packages and containerized services early in our software development process and address them before they reach a customer environment.
Secure vault for centralized secrets management
Studio uses Vault, a tool provided by HashiCorp, for securely managing all secrets across the platform, including API keys, passwords, and certificates. Key/value pairs are encrypted prior to storage, adding an extra layer of security for data at rest.