Path to Secure Linux Platforms
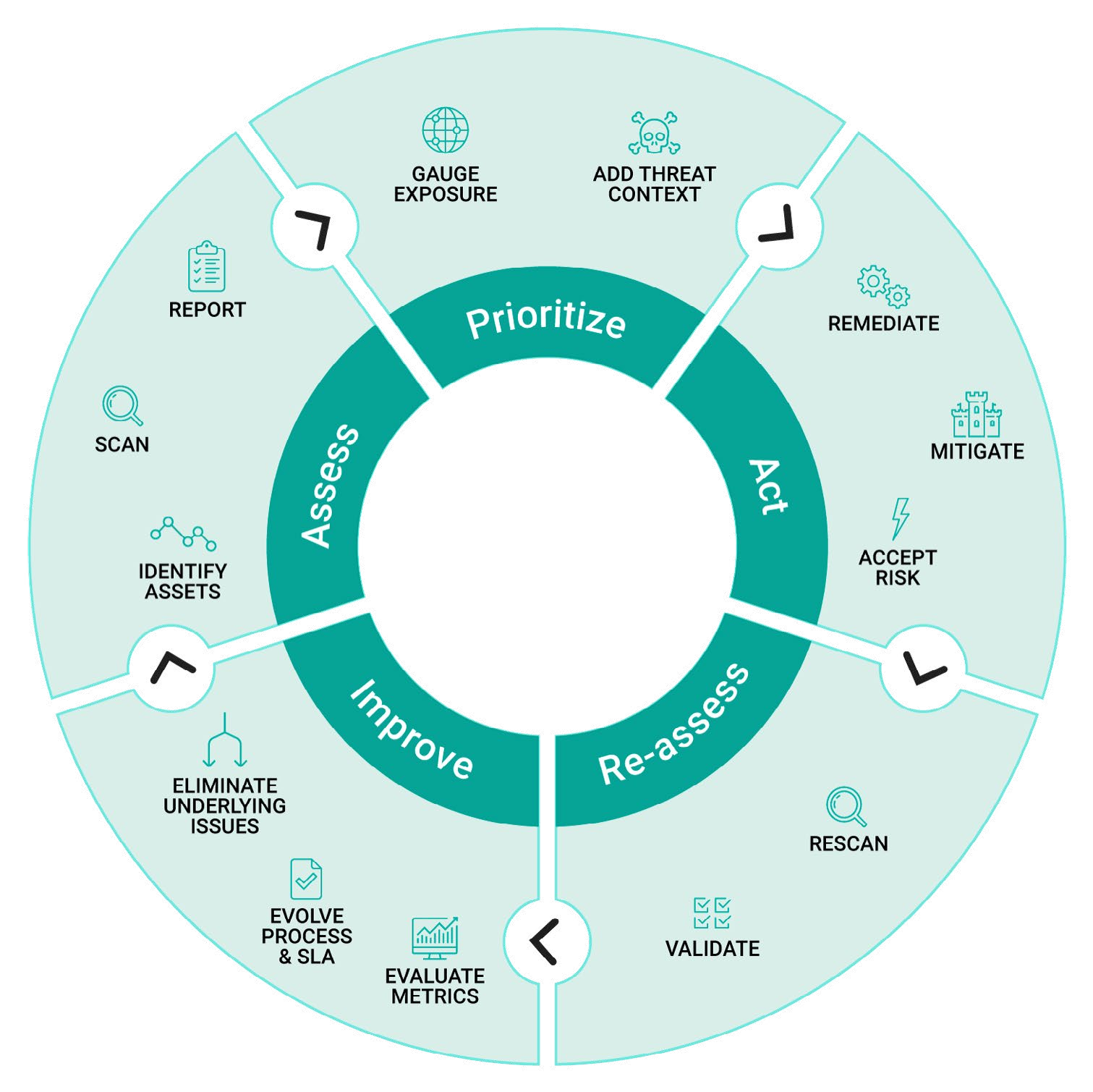
The vulnerability management lifecycle: A continuous improvement process model for software solutions
Remediate, mitigate, and determine risk
- The good news is, you can leverage a partner like Wind River to perform the fix for you. As you evaluate partners, look for one that has worked with multiple platforms, already has a fix ready that has been validated on your version, has solved this fix before, and can do it again. Ideally the solution has already been tested extensively and proven effective. Additionally, evaluate a potential partner for speed, accuracy, and responsibility. Your partner should be able to not only help with the standard version of the issue at hand but also solve for the issue as it pertains to your particular solution.
Mitigate
- When you choose to mitigate, you are adjusting your solution to make the issue less harsh or hostile to your environment. You can make the offending aspect of your solution irrelevant (remove the impact), firewall it (put something in the way like creating a self-check in your software), or remove it completely.
Accepting the Risk
- Accepting the risk involves understanding the probability of occurrence (what are the odds?), understanding the impact if the issue is not correctly fixed, and evaluating the effects of the speed with which a solution is deployed; the longer a vulnerability is out there the more of a risk it poses.
4. Reassess
Once you’ve acted by either remediation or mitigation, it’s time to reassess. Do a rescan of the what you did to evaluate it and validate what worked.
Rescan
- Reassess assets to produce another manifest file or SBOM that incorporates the changes that you’ve made. NOTE: Remember, relying merely on a manifest file will be a challenge because it only knows about the version and provides limited information to your security team. If you use an SBOM you might actually be able to track the patches that have been applied to your solution.
- It’s vital that you stay current, whether with the SBOMor the CVE knowledge base. Having updated results enables you to efficiently triage the vulnerabilities as they’re coming in while making sure you’re being effective in remediating or mitigating the CVEs that you’re addressing.
- A critical component of a re-scan is making sure that your partner solution integrates with your DevOps — it needs to be able to understand the whole bug tracking lifecycle for your solution and have that info automatically feed into your scanner.
Continually evolve process and eliminate underlying issues
Validation
- Whether your remediation involved back porting or up-revving, it’s important to validate that it was successful. Both involve new variables — back porting comes with new code and up-revving comes with new features and possibly new CVEs and packages.
- When you up-rev, adding other packages could make it necessary for you to update your application as well to use the new interfaces brought on by these new packages.
- Testing to determine whether the CVE has been fixed can be challenging. A lot of CVEs are almost theoretical in nature and as a result do not have an easy test case to show whether or not the vulnerability has actually been resolved.
- Once a CVE has been addressed, the common course of action is to run a smoke test designed to answer the question: does your solution still do what it’s supposed to do, and function as expected? Once you’ve ensured that, you progress through integration testing, regression testing, system and full end-to-end testing. Whatever Semi vendor or partner you are using, make sure it is running all these tests.
5. Improve
You’re going to run this process again. Once you’ve completed the cycle, this stage looks at how you can improve upon your lifecycle.
Evaluate Metrics
- Were your metrics for success appropriate to gauge the outcomes of your vulnerability response? For example, you may choose to re-evaluate the manner in which you measure how quickly and accurately the validation went.
Evolve Processes & SLA
- Develop a plan to improve your processes and SLA (the service level agreement between client and customer) to address the CVEs and reflect changes.
Eliminate Underlying Issues
- Get to the root of any underlying issues to set y ourself up for success as you redeploy your process.
In Closing
The Linux Foundation reports that, “It has been estimated that free and open-source software (FOSS) constitutes 70% to 90% of any given piece of modern software solutions.” Companies are becoming more aware that as they use open source software they need to identify dependencies on the open source components that they’re using.
These companies need to proactively and regularly monitor all components for usability, trustworthiness, and vulnerabilities. The key takeaway here is it’s a never-ending process — you’re always evolving, always improving.
But many companies are falling short. According to the Open SF Foundation, 50% of companies have a security policy, 30% do not, and 17% of respondents didn’t know if they had one or not.
Companies need to adopt best practices for every stage in the vulnerability management lifecycle and have a CSIRT (computer security incident response team) who can understand the impact of a vulnerability and notify your customers to explain what you’re doing about it.